While advancing technology has led to many incredible security improvements in recent years, key fob systems are by far one of the easiest and simplest innovations yet. A key fob entry system combines physical hardware and sophisticated software into a convenient modern package.
Key fob systems are easy enough for everyone to use. In fact, if you have visited a hotel within the last few years, you have likely used this tech yourself to access your room. In addition to the aesthetic perks, key card security systems keep unwanted intruders out while also assisting visitors in real time.
When you need to protect your home or business, contact Alarm New England for a free quote. Discover how we can set up a customized, secure key fob system to suit your needs.
How Do Key Fob Entry Systems Work?
Key fob door entry systems may look different from model to model, but most operate under the same basic principles. The process for using these systems generally includes the same steps:
- Your security card and key fob use electromagnetic or radio wave technology to emit certain wireless signals. You can customize these signals with unique credentials for every user who needs access.
- The access reader system is installed at key entryways, normally right by the door for easy access.
- Anyone wishing to enter the restricted area must first present their credentials. Some key cards only need to be in proximity to the access reader, while others require swiping through a card reader.
- The reader communicates with the card and key fob via wireless signals to verify the credentials. The verification process will vary based on the model of the key card access system.
- If the system recognizes and approves the credentials, the access reader unlocks the door and allows entry.
The process is simple, efficient, and quick. There’s no need to worry about making multiple copies of metal keys, manually paging in visitors, or constantly changing passwords. Instead, users can swipe their cards, scan their credentials, and get on with their work.
Types of Key Fobs and Key Card Access Systems
While all card and key fob systems use similar technology, many types of key access systems are on the market. The best one for you will depend on your security needs and personal preference.
Electromagnetic key cards
Electromagnetic key cards (like Wiegand and swipe key cards) require physical interaction with the reader to work.
Wiegand key cards
Wiegand key cards are one of the oldest versions of electronic key cards on the market today. In these systems, magnetic polarization and specially-made wires transmit data. This data can be almost anything (such as credit card information or medical data) and provides the basis for much of today’s access control tech.
The user usually swipes their Wiegand card through the reader, where the magnetic field in the reader interacts with the wires in the card. These wires will react, and when the wires change in certain ways, the reader translates these signals as the owner’s credentials.
Swipe key cards
Like their Wiegand counterparts, swipe key cards have a magnetized strip coded with a unique pattern. Users swipe these cards (like a credit card) for access. The readers automatically detect predetermined patterns as authorized credentials.
Unlike Wiegand cards, system administrators can wipe and recode swipe cards to program different credentials or rewrite them to work with a separate lock.
Radio frequency cards
Another class of key card access systems uses radio frequency technology to assign credentials.
RFID key cards
Radio-frequency identification (RFID) key fobs and cards emit radio waves to communicate their credentials. The card readers send signals via excite fields. When the corresponding RFID cards are in range of these fields, they relay a signal back to the reader to open the door.
Proximity key cards
Proximity cards work similarly, except their radio frequencies are different from the RFID cards. Users also need to be close to the card reader for the signals to connect.
Passive readers use radio frequencies and require cards to be held closer to the reader to work. “Active readers, on the other hand, generally have their own power source (such as a lithium battery) and work at longer distances.
At Alarm New England, we have experience designing, customizing, and installing both electromagnetic and radio frequency key fob systems. In your consultation, we will discuss your needs to create a key card system suited to your building.
Benefits of Commercial Key Fob Door Entry Systems
Due to their compact size and their prevalence on the market, many companies use these key card systems for business operations that require automated and restricted access. Rather than using biometrics or cumbersome passwords, key fob systems let business owners implement intelligent security measures that still have the same ease as a regular lock and key.
Key fob door entry systems offer many other convenience and security benefits.
Simplified access control
Business owners can quickly and easily add or remove access for individuals from a single dashboard. This makes it easy to:
- Upgrade a user to access more restricted areas
- Quickly onboard a new hire
- Allow temporary access
- Activate new cards in bulk
- Program cards to deactivate automatically after a certain date
Automate access rules and schedules
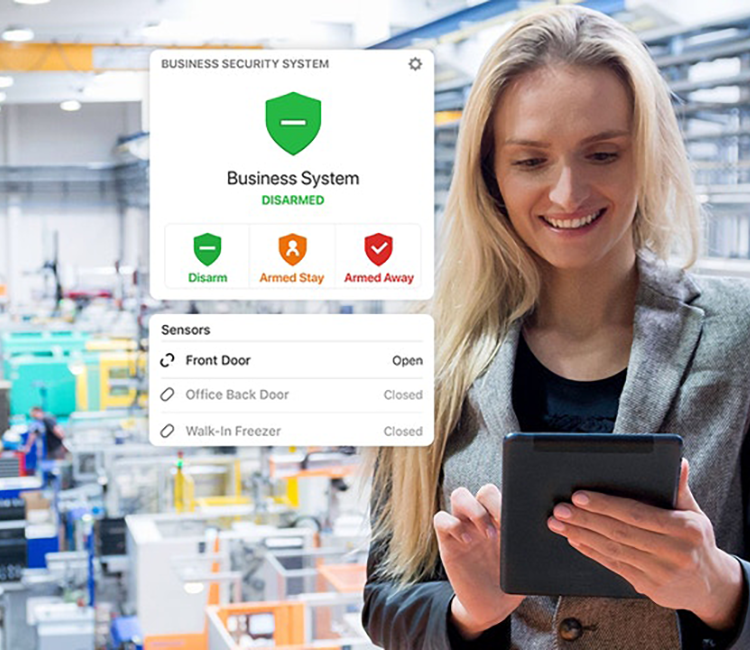
Key access systems combine the functionality of the physical card with the convenience of an automated system. In addition to unlocking automated doors, users can program their security system to arm and disarm in response to designated employee badges.
Your first employee can disarm the system easily when they first come in for the day, and with a simple double tap of their card, they can arm the system again on their way out of the door.
Intuitive for employees or tenants
Key card systems are easy to use. They completely avoid some of the difficulties of other security measures. Tumbler locks and metal keys are bulky and difficult to operate in poor weather, but tapping your fob against an electronic reader is simple and fast.
As electronic security measures grow more and more popular, having a key card that fits in the credit card slot of your wallet makes life easier for everyone. Most people already know how to use a key card from their own travels, and if they do not, teaching them the process is quick and easy.
Easy administration
Commercial key fob door entry systems help business owners automate their security measures while still giving them the option to track their progress. This trackability is crucial to ensuring your security measures are working as designed.
If breaches ever happen, managers can quickly look up the data for specific readers and see where the disconnect occurred. They can monitor which doors opened, for how long, and who opened them.
If a user ever loses their key card, replacing it is quick and easy. The manager can deactivate their card immediately and reissue a new one with new credentials, which is much faster and cheaper than replacing the entire lock!
Key Card Access Systems for Small Business Security Needs
At Alarm New England, our experienced technicians design, install, and service key card fob systems for businesses of any size.
Key access security locks give small business owners better control over their assets. If you’re constantly on the go, this awareness lets you make informed business decisions anytime, anywhere.
Where can you use a key fob system?
These units are versatile at any scale, even with only a few access readers and a minimal portfolio of access cards. Some common scenarios include:
- Many establishments install access readers outside of employee-only entrances, such as entryways for kitchens and staff-only break areas.
- Businesses with large equipment storage areas (especially those with high-value assets, like computers or construction equipment) install access systems to prevent theft or misuse by employees.
- Private communal living areas, such as college dorms or apartments, employ key card access systems to ensure the safety of their residents.
- Companies with physical file storage, such as small medical clinics or real estate offices, need to ensure that only trained employees have access to these documents.
What can fob key card access systems do for you?
Key fob systems let any business control who has access to their space, staff, and information. Using time-tested electromagnetic technology, these access systems have exponentially improved in recent years, offering users a more streamlined and customizable experience.
These systems are perfect for users who still prefer a physical component to their security measures. Key cards are easily programmed, easy to use, and just as easily replaced if the original card ever gets lost or stolen. This convenience helps lower your operational costs, all without sacrificing your physical security and peace of mind.
If your business could use an efficient and effective key card security system, consider what key fob access control systems could do to keep you safe and productive.
Call Alarm New England at 857-445-4010 to discuss your security and alarm needs and discover what our family-owned, locally operated alarm company can do for you.